
ISO Certified Company - Google Rated Number 1
cyber security inplant training
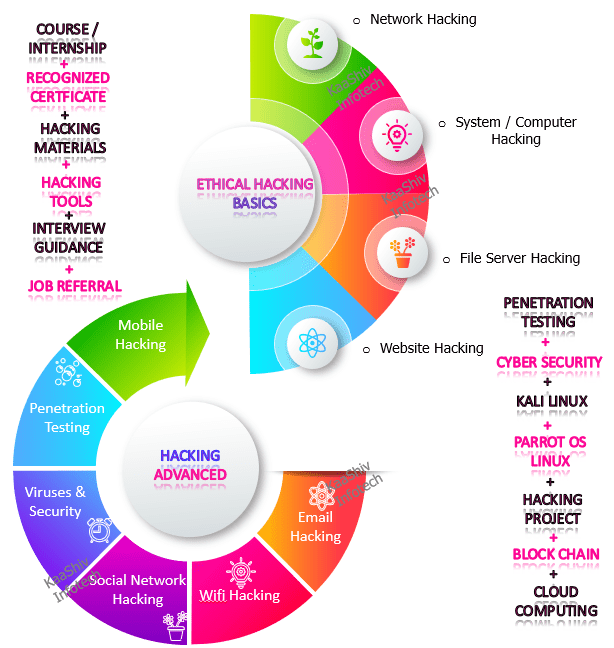
KaaShiv Infotech offers, cyber security inplant training . Inplant Training provides you an in-depth knowledge of Cyber Security. This training enables the students to understand and learn the current trend in the job market. Students will prefer online inplant training to build their profile for their jobs and also for their higher studies. Our company provides both offline and Cyber Security Training Online . cyber security inplant training in chennai – imparts technical and programming skills on the below list of hacking areas such as,
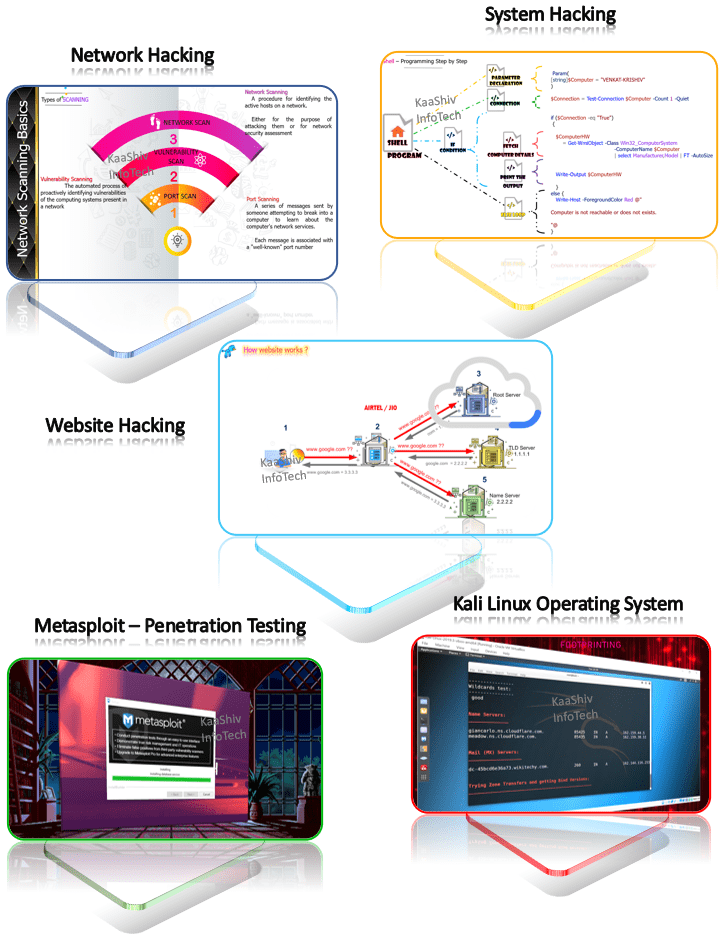
- Network Hacking
- Command Shell Hacking
- System Hacking
- File Server Hacking
- Web Server Hacking
- Website Hacking
- Mobile Hacking
- Penetration Testing
- Social Network Hacking
- Email Hacking
- Wifi Hacking
Highlights of our company
- Common Wealth Bank Recognized Leading Light Rising Star Award Winner
- Run by 10 Years Microsoft Awarded MVP ( Most Valuable Professional )
- Google Recognized Experts and Cisco Recognized Certified Experts
- Microsoft Certified Professionals
- Artificial Intelligence and Robotics Experts
cyber security inplant training 2021 india
Why our company provides, cyber security inplant training for college students
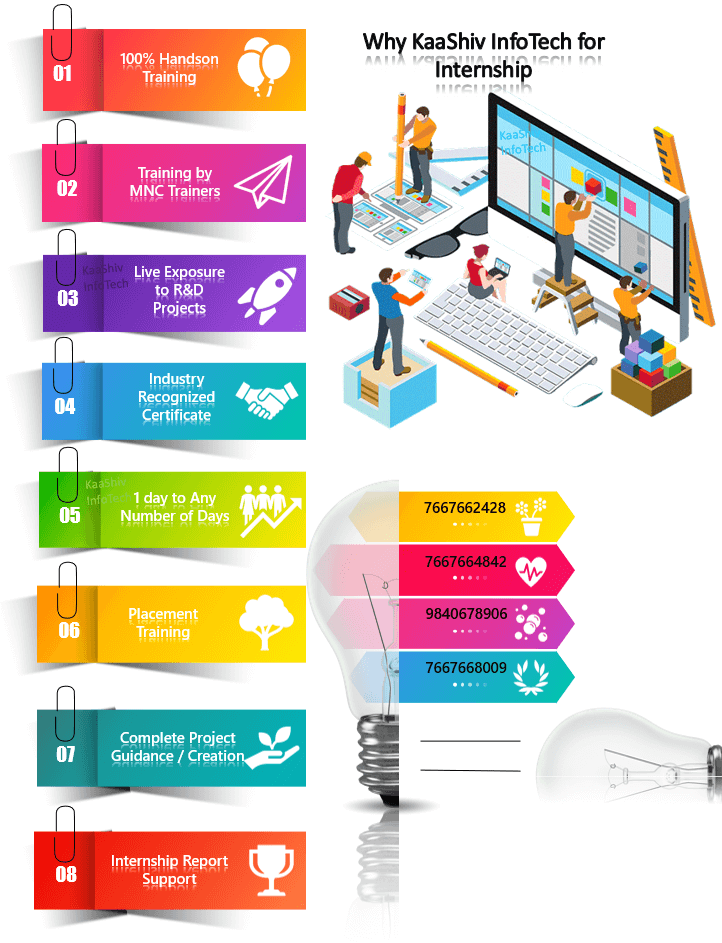
The Course curriculum for, cyber security virtual training – is carefully researched and prepared by professionals from MNC to meet the demands expected in the current IT industries. After completing Inplant training in Chennai at KaaShiv Infotech, students will be familiar with the entire ethical hacking, cyber security, Implementing a hacking project. Below are some of the insights of our program, cyber security inplant training in chennai ,
Trainers to train you
Our, Cyber Security inplant training in India – Program Trainers are real-time IT experts and cyber security professionals worked in leading MNCs like
- TCS,
- HCL,
- Infosys,
- Cognizant,
- Wipro

Cyber security inplant Training objectives
- Inplant training are useful in about any industry, and cybersecurity is no different. There is an extreme shortage of qualified and experienced cybersecurity experts.
- Inplant Trainings are one way to get new cybersecurity graduates the experience they need to move right into the workforce. When it comes to cybersecurity, there are many things to consider, including whether a government inplant training or a private company makes the most sense.
- It’s more likely that a private company will provide a reward for inplant training . However, for students interested in pursuing a full-time career within the government sector, obtaining a cyber security inplant training in government – would be the most beneficial.

Benefits of Doing cyber security inplant training
Inplant trainings help to getting a chance to try all the possible jobs with explore different options in career.
- Cyber security inplant training would be to –
- Use different strategies to penetrate the security system for finding potential vulnerabilities or errors that can be exploited.
- Recommend better ways to improve the current security posture.
- Co-operate with developers or other security professionals to advise on security needs and requirements.
- Train the staff against different malicious cyber traps.
- Finding the vulnerabilities and improving the security system consumes the major part of an ethical hacker’s life .


cyber security internships work from home
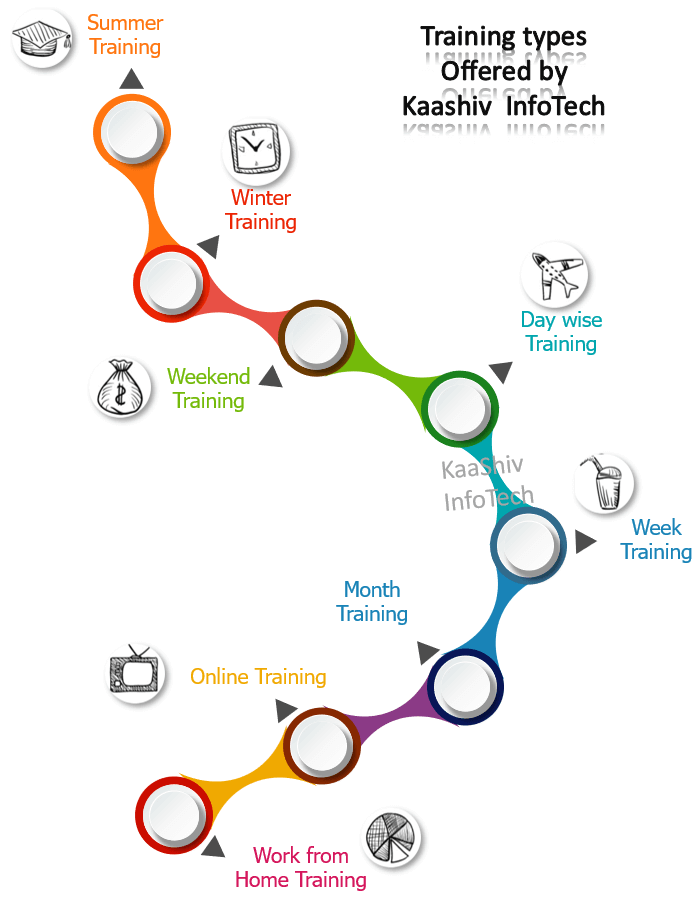
Types of Inplant Training to the Students
Learn and Implement
45 Concepts Covering 7 Technologies
+ 1 Projects
Short Term Internship
- Cyber Security Inplant Training
- Cyber Security Inplant Training – Duration: 1 day, 2 days, 3 days, 5days/ 10days or Based on Student Preference
- Training hours: 3 hrs per day
- Software & other tools installation Guidance
- Hardware support
- Cyber Security Inplant Training Report Creation / Cyber security Projects
- KaaShiv Infotech is top under , online cyber security internship , 1 Real time projects – After 6 months of regular Paid Inplant Training, Training becomes free + For best interns Stipend will be provided + Best Interns will be offered Job too.
- Inplant Training Certificate & Industrial exposure certificate + (Achievement certificate for best performers)
S.No |
Best Cyber Security Course – Syllabus100% Practical – Live HandsOn – cyber security inplant training in chennai |
|---|---|
| Topic 1 : | Ethical Hacking Basics
( Introduction Hacking , Job Openings, Mega Breach History , Hacking Terminologies , Elements of Information Security, Motives of Information Security, Information Security Threats Categories , Hacker Classes , Website Info Extraction , Penetration Testing , Bot Website , Website Directory Extraction , SQL injection , Hacking Social Data )
|
| Topic 2 : | Network Hacking
( What is Networking? , Network Scanning Basics , How Network Scanning Works ? , Types of SCANNING , THREE WAY HANDSHAKE , ICMP SCANNING , PING SWEEP SCANNING , TCP Communication FLAGS , Full Open Scan , Stealth Scan – Half-Open Scan , UDP Scan , Check Live System , What is Port Scanning , Lists of Ports , Check Open Ports , Network Mapping , Proxy Servers , Counter Measures )
|
| Topic 3 : | Command Shell Hacking
( What is Operating System , Famous Operating System , Shell Programming, Basic Requirements for Shell , Fetch Computer Hardware, Fetch Computer Total Memory , Fetch Computer RAM Memory, Fetch Hard Disk Details , Command to get system information , Utility to get System Information , Bypass Windows Default execution & increase , Process priority , Installing Packages Using PowerShell , Powerful Copy Command , Fetch RAM Memory Details , Fetch RAM Memory HW Details , Fetch Driver Details , Free Format of Folder Listing , Get list of Tasks Running in Computer , Get list of Services Running in Computer , Delete Files using PowerShell , Delete Folders using PowerShell , Find User Last Login Details , Restart Computer using PowerShell )
|
| Topic 4 : | System Hacking
( How to find IP Address of a Computer , How to find IP Address of a Website Calculate How much data transferred in a network , How to find the path of accessing the website , Find IPV4 and IPV6 details of the Website Server ? , Find Wifi Status , Find Wifi Security Info Find Wifi Password , Get the MAC Address from IP Address , Flush the Network Connection ,Tool to find the Website Owner Details , Tool to Check Website is Alive or not , Tool to Check Computer Information’s heart beat , Tool to Check Processes individually , Check for Windows For errors ,Making Password Never Expires , Find the Security ID of the User , Access Control Panel as a Specific User , Tool to Fetch Complete PC Information , Find the Security ID of the User , Access task Manager information from Tools , Tool to find Users Logged in to the System , Hack Administrator Account , Hack Windows Bypassing using USB , Hack Windows By confusing , Virus Check Software , Memory Hijack Software , USB injection Software Driver Check Software , Browser Clean Software , What is Volume Licensed MS products , Ccleaner – memory cleanup , Malware Threats , Viruses Hacking , Resident Virus , Direct Action , Boot Sector , Multi Partite , Polymorphic , Overwrite , Space Filler Virus , System Hacking Types , Viral Scripting , Hardware Hacking )
|
| Topic 5 : | File Server Hacking
( Anatomy of a FTP Server , How File Transfer Protocol ? , How to move Files to Live Server , Use Specified Authentication to load the Files into Live Server , Check for the port to move data , Using Anonymous Authentication is not secure, Open FTP with Server Name , Anatomy of a FTP IP Address , Open FTP with IP Address , Secure FTP server from Hacking , HTAccess or Any config files , Mobile Memory Access Via FTP Concept )
|
+ Cyber Security Inplant Training Certificate
+ Free Industrial exposure certificate + (Achievement certificate for best performers) + 1 Cyber Security Project
Learn and Implement
70 to 400 Concepts Covering 9 Technologies
+ 2 Projects
Long Term Internship
- Cyber security inplant training
- Cyber Security Inplant Training – Duration: 6 days to 6 Months or Based on Student Preference
- Training hours: 3 hrs per day
- Software & other tools installation Guidance
- Hardware support
- Cyber Security Inplant Training Report creation / Cyber Security Project Report creation
- KaaShiv Infotech is top under, Online internship in cyber security , based 2 real time projects.
- 2 Certificates will be given
- Inplant Training Certificate
- Industrial exposure certificate
- + (Experience Letter for best performers and Researchers)
- Free cyber security internship / Cyber Security internship free – After 6 months of regular Paid Inplant Training , Training becomes free + For best interns Stipend will be provided + Best Interns will be offered Job too.
S.No |
Online Cyber Security Course 100% Practical – Live HandsOn – |
|---|---|
| Topic 1 : | Ethical Hacking Basics ( Introduction Hacking , Job Openings, Mega Breach History , Hacking Terminologies , Elements of Information Security, Motives of Information Security, Information Security Threats Categories , Hacker Classes , Website Info Extraction , Penetration Testing , Bot Website , Website Directory Extraction , SQL injection , Hacking Social Data ) |
| Topic 2 : |
Network Hacking
|
| Topic 3 : |
Command Shell Hacking
|
| Topic 4 : |
System Hacking
|
| Topic 5 : |
File Server Hacking
|
| Topic 6 : | Web Server Hacking ( What is Root Name Server , How website works ? , How website works ? , How DNS Works , How Dig Tools Works , Server Info Extraction Tool – Part 1 , Server Info Extraction Tool – Part 2 – DNSKEY , Server Info Extraction Tool – Part 2 – DS Record , Anatomy of a Website , How Internet Works , How Website Works , NSLookup Networking Command , Diggint Tool , How to make a Server ? , Server into a Web Server ? , Web Server to World Wide Web Registered Server ) |
| Topic 7 : | Website Hacking ( Information Gathering – FootPrinting , DNS Enumeration , DNS Info Extraction , What is DNS , What is Reverse DNS , Chrome Extension , IP Information of the Website , SPF Record Details , Web Server Information , Website Owner Information , Termux ReconDog , Install Python&GIT , Port Scanning , Who is Lookup , Who is Lookup with software , Who is Lookup with websites , Port Scanning , Honey Pot Server , Reverse IP Lookup , Reverse IP Lookup with websites , Censys – Website Monitor tool , What is Web Session ? , What is Session Hijacking ? , Tor Browsers , Anonymizers , Type of Anonymizers , Anonymizers – Bypass Web Filters , Anonymizers – Bypass Internet Traffic , What is Phishing , Phishing Prevention , What is IP Spoofing , How IP Spoofing works ? , IP Spoofing Basics – How it works ? , IP Spoofing types , IP Spoofing Types – Non-Blind Spoofing , IP Spoofing Types – Blind Spoofing , IP Spoofing Types – Smurf Attack , IP Spoofing Types – MITM Attack , IP Spoofing with Software’s , IP Spoofing with Websites , What is MAC Spoofing , Remote Access VPN , How VPN protocol works ? , VPN Data Encryption , PC VPN Settings , Mobile VPN Settings , IP Spoofing with VPN , How to get Current Ip address ? , Secret mobile Settings for VPN configuration , VPN network configuration with new IP , What is VPN , What is Firewall – Technical Info , IP Spoofing Prevention Technique , Additional Features of Firewall , Firewall Types , Host Based Firewall , How Router works ? , Network Based Firewall , What is Cloaking in Hacking ) |
| Topic 8 : | Mobile Hacking ( Find mobile number details , Access Mobile Number information , Basic Phone Info Package , Install Termux , Access Memory using Termux , Hacking Mobile Task Manager , Networking Cmds in Termux , Ping Command in Termux , Botting Websites , What is an Internet Bot ? , What is a Website Bot ? , What is a BotNet ? , How Hackers attack Website – DOS Attack , How DDOS works , Charter – AntiBot Scanner , Microsoft Safety Scanner , Website Directory Extraction , What is Web Server , Vulnerability testing , Website Vulnerability Analysis ) |
| Topic 9 : | Penetration Testing ( MetaSploit – PenTest Tool , What is MetaSploit , MetaSploit History , MetaSploit Packages , MetaSploit Modules , MetaSploit Sub Modules , How MetaSploit works with Pen Testing , How Exploits works in Metasploit ? , Metasploit Architecture , Metasploit Library , Metasploit Codes , Metasploit Tools , Metasploit Command Basics , Modules in Metasploit , Create and Setup Exploit, Attack Target , Fetch the injected Virus Path , Make Directory to Control Target , Injecting Files in to the Target Machine , Idle time and IP Details of the Target , Keyboard Hacking/Password Attacks , Audio Recording , Hacking Screenshot of Target , Hacking Screen of the Target , Hack Camera Details in the Target , Hack Camera Take snap of the Target , Hack Camera Take Live Video of the Target , How to install Metasploit in Mobile , How to search Metasploit packages , Find open ports using Metasploit in target ) |
| Topic 10 : | Social Network Hacking ( find fb id , Find facebook friends using termux – Facebook Tricks ) |
| Topic 11 : | Email Hacking ( Email Spoofing , Mail Tracking with gmail , Send mail to find location ) |
| Topic 12 : | Wifi Hacking ( Wifi Introduction – Basic components of Wifi , How Wifi works , Wireless Devices, Get Basic Wifi Accounts Stored in the Computer , Get Wifi interfaces Stored in the Computer , Get Wifi Properties Stored in the Computer , How to Export Wifi Passwords , How to get Windows Wifi Password ) |
| Topic 13 : | Kali Linux – Hacking Operating System ( Introduction , FootPrinting Tools, Backdoor Attack Tools , Reconnaisance Tools , Sniffing Tools ) |
| Topic 14 : | Parrot OS – Hacking Operating System ( Anonymous Access – Be a Hacker , No one can hack you , Control your network usage , Control your computer Execution , Control anyone in the Network ) |
+ Cyber Security Inplant Training Certificate
+ Free Industrial exposure certificate + (Achievement certificate for best performers) + 2 Cyber Security Projects
Ethical Hacking training in chennai
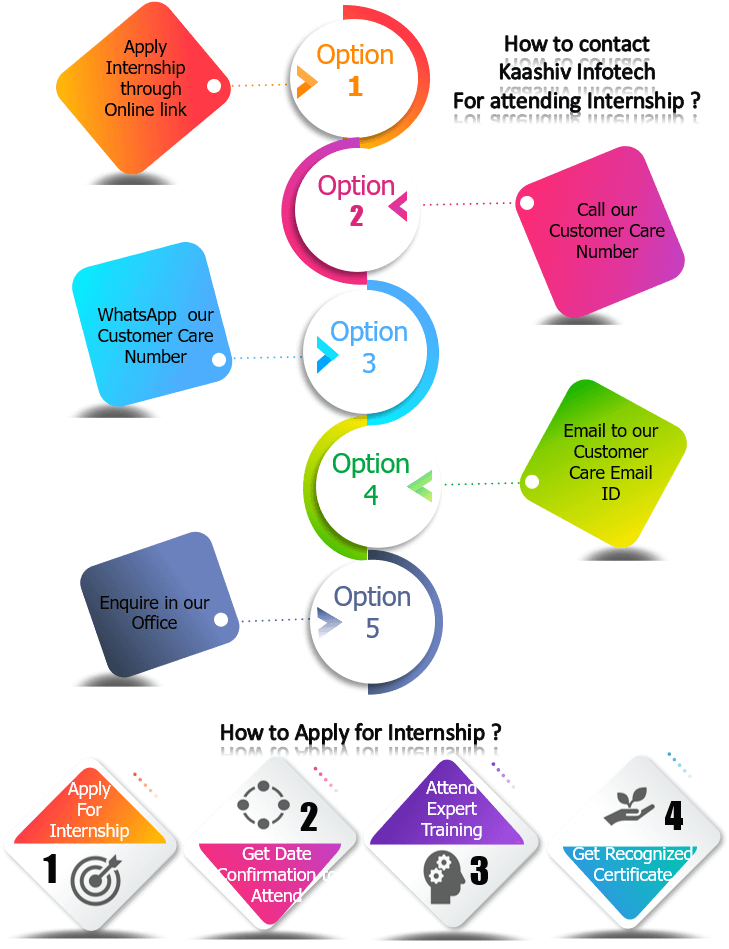
Apply for Inplant Training - Contact Us
Contact Number / Whatsapp Number
Mobile 2 : 7667664842
Mobile 3 : 9840678906
Hacking Internship
Sample Video – Online cyber security inplant Training
Cyber Security training and internship – Demo Link :
Check out our Sample Content under the topics ” Become a Cyber Security Expert – Online Cyber Security Course “
Check our Previous testimonials from students from Different Countries and Different States :
Check our students, Internship feedback kaashiv infotech reviews
More about our Company
Hacking inplant training
Our, Online Inplant Training for Cyber Security - Training Youtube Channels –
Our Technology Channel :
https://www.youtube.com/channel/UC2MYZHG8a56u4REI2RedtRA
Our Subject Channel :
https://www.youtube.com/channel/UC9dcBYLL-ZGTy7ml8YMTlag/videos
Check out the colleges attended our Internship :
Click to view more details kaashiv infotech inplant training reviews
Intern Students Feedback
Check our ( Intern )Students Feedback :
Inplant training in chennai for Cyber Security – Feedback – https://www.kaashivinfotech.com/inplant-training-feedback
Cyber Security Internship – Feedback – interns for cyber security students
Our Live Project:
We ranked Top 2000 technological companies in India, www.wikitechy.com

YEARS OF EXPERIENCE COMPANY

PROFESSIONAL EXPERTS
/ TRAINERS

SUCCESSFUL COMPLETED STUDENTS

COLLEGE
STUDENTS
PARTICIPATED
1. Report for the inplant training will be provided after the completion of the programme.
2. Regular tech updates to the students.
3. Free inplant training Projects given
1. Industry Recognized, certificate for internship will be given.
2. Certificates will be given ( Inplant Training Certificate & Industrial exposure certificate ) + (Achievement certificate for best performers)
2 day / 3/ 4 / 5 / 10, 20 days or 1 month to 6 Months ( Any Number of Days – Based on student preferences)
Specialized technologies from, cyber security inplant training
Ethical Hacking training in Chennai
cyber security internships for college students
Cyber security inplant training for beginners
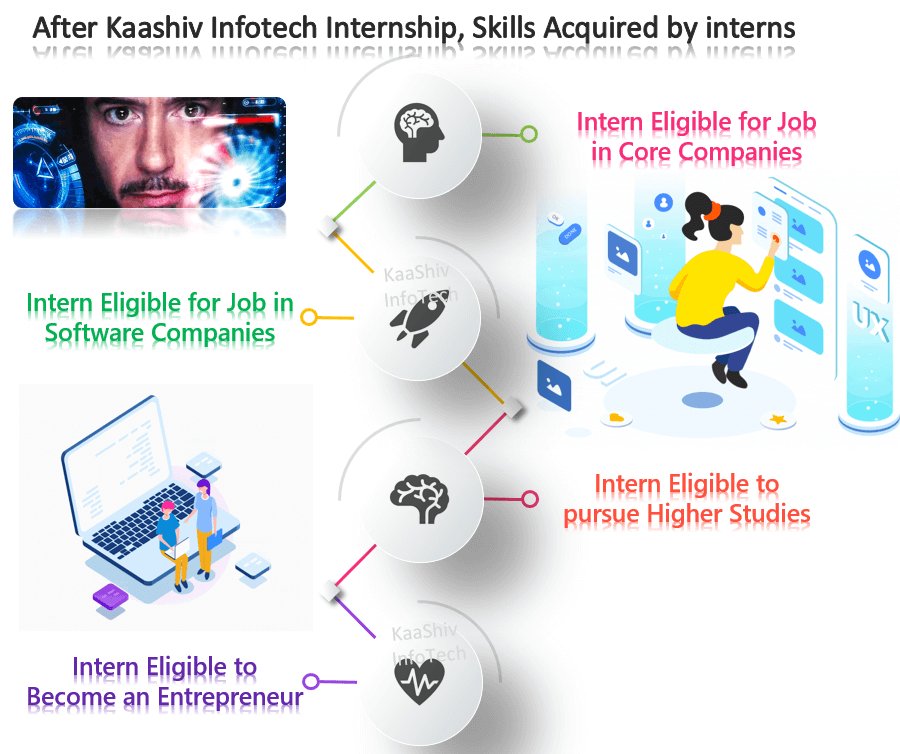
- cyber security inplant training for freshers – Cyber security inplant training , can be done by the freshers to build their career. This program will provide a clear baseline for the entry level engineers to enter into the IT industry.
- Before entering into the companies, doing the training will give you more clarity in the programming field.
- Kaashiv Infotech recommends all department students, fresher, and even school students to take up this online training and build their careers.
Cyber security summer inplant training
- This program becomes mandatory before completing their degree for computer science based students Due to its huge involvement and implementation flexibility in many fields.
- The reason for doing inplant training is, real time industrial exposure is preferred by most of the companies in India. Identifying a real time training with a recognized inplant training certificate is very important. After completing the inplant training will acquire practical knowledge, analytical skills, programming skills and problem solving skills.
Cyber security winter inplant training
- Inplant training can be done by diploma studying students , engineering students or freshers and arts college students too.
- We are inviting highly excited students, who are interested in winter research & development program. The selected students will have the chance to work with Kaashiv Research & Development team. In this cyber security inplant training, the students will also have the chance to join in the workshops, events, live projects of the main industrial research organization in the world and network with other students in different fields from another field.
- This Cyber Security Winter Inplant Training makes your career in IT Security.
Cyber security winter inplant training
- Kaashiv offers inplant training for the students or professionals who prefer, cyber security inplant training work from home .
- Cyber Security intern will be learning cutting edge technology based on cyber security online classes .
- Our, inplant training in cyber security online – programme provides Online portal to study anytime, online classes to study flexibly , industry recognized certificate with, cyber security training questions for all the attendees.
- Most of the students will be getting ready for campus placement or off-campus interviews.
- Applying basic theoretical ideas into the real world via inplant training programs horne their skills to the next level of industrial knowledge.
- Outcome of this , cyber security Inplant Training is :
- Student will be specialized in cyber security and ethical hacking programming.
- Students will be getting trained in / writing 10 Programs – Will change based on the duration of the program.
- 1 Project and project report will be given at the end of the program.
More Questions on Cyber Security Inplant Training
What are some good places to learn Cyber Security Inplant training in Chennai ?
- Kaashiv Infotech is the best place to learn Cyber security training where the training is provided with real time example.
- The Cyber security inplant training in Chennai Syllabus is designed according to the student needs of the corporate client, which will definitely help you to clear the interviews easily.
What skills are needed for cyber security ?
- Problem-Solving Skills
- Technical Aptitude
- Knowledge of Security Across Various Platforms
- Communication Skills
- Fundamental Computer Forensics Skills
- An Understanding of Hacking
Who is my Cloud Computing trainer and how they are selected ?
- Our trainers are more than 10+ years of experience in course relevant technologies.
- Trainers are expert level in the subjects they explain because they continue to spend time working on real-world industry applications.
- Trainers have skilled on real-time projects in their industries.
- Are working professionals working in international companies such as CTS, TCS, HCL Technologies, etc…
- Trained more than 1500+ students in a year.
- Strong theoretical & practical knowledge.
Can you learn cyber security online ?
- Learn Cyber Security skills online with Kaashiv . Kaashiv infotech is the world’s leading IT and cybersecurity online training network offering in-depth ethical hacking courses, for beginning, intermediate and advanced hacks.
Can I do cyber security from home ?
- There are few chances to work from home in cybersecurity such as cybersecurity research, security consultancy, audits, penetration testing, IAM analysis, security architects, etc. Due to the increased responsiveness of cybercrime, the request for specialists who can protect the business’s digital space is increasing quickly.
Why You Should Enrol for Inplant training Program With Kaashiv InfoTech ?
- Learn from top Internship company
- Globally Accepted Degree
- Flexible learning – Anytime Anywhere Learning
- Preferred Destination for Corporate Hiring
What soft skills are needed for cyber security ?
- Strong Research and Writing Skills
- Collaboration
- Adaptability
- Networking
- Problem Solving
Is python needed for cyber security ?
- Python is a useful programming language for cybersecurity because it can achieve many cybersecurity functions, including malware analysis, scanning, and penetration testing functions. It is user-friendly and has an well-designed simplicity, making it the perfect language choice for several cybersecurity specialists.
Does cybersecurity need coding ?
The majority of entry-level cybersecurity jobs do not need coding skills. Though, being able to write and understand code may be essential in some mid-level and upper-level cybersecurity positions that you will become qualified for after you’ve built a few years of experience.
Is cyber security a good career ?
Even though a job in cybersecurity can be highly satisfying, it can also be very interesting and stressful. Understanding some of the job responsibilities, as well as the features and nature traits of these jobs, may help you decide if a career in cybersecurity is right for you.
Which startups provide the best , cyber security inplant training in India ? What are the duration of these inplant training ?
- The Answer is, Kaashiv Infotech offers inplant training . This inplant training involves, practical knowledge and real time experience . Inplant training duration can be from 1 day to any number of days like 6 months.
How to get training in Cyber Security ?
- The answer is – Kaashiv infotech provides, training in cyber security . This training involves learning and developing applications. Various technology trainings are,
What are the requirements for cyber security inplant training ?
- There are no specific degree requirements used as prerequisites for cybersecurity jobs. However, most managers will be looking for a bachelor’s degree in computer science, cybersecurity, or a related technical field.
cyber security internship requirements
- Are enrolled in a degree program at the time of the internship
- Have completed their Foundation year (at least 27 credits)
- Have a cumulative GPA of 2.5 or above
- International students also have specific eligibility requirements.
What do cyber security interns do ?
- This contains tasks like reading and responding to emails, establishing documents or other digital resources, studying and reviewing the company’s present IT policies, and researching new security products and strategies.
- In addition, cyber security interns may also take part in projects that are more specific to cyber security.
How to Describe Your Cyber Security Experience ?
cyber security internship job description for resume ( cyber security internship resume )
- Perform technical evaluation and penetration testing of internally- and commercially-developed applications (web, desktop, and mobile), systems, and medical devices.
- Support in developing the security controls for IT solutions of all types (mobile, web, client-server, etc).
- Maintain knowledge of security vulnerabilities, threats, and industry standard methodologies.
- Participate in suitable and relevant sessions and courses to maintain technical proficiency.
- Assist in developing and implementing an annual personal education plan to develop and maintain currency of security-related skills, technologies, methodologies, and standard methodologies.
How About, cyber security inplant training cover letter ?
cover letter for cyber security inplant training
- Start your Cyber security inplant training cover letter with a compelling opening statement.
- Tell them why you’re the perfect candidate to resolve their future cyber concerns.
- Clarify why this specific company and position are ideal for you.
- Close it with a call-to-action as simple-but-powerful as a brute-force attack.
How much does cyber security get paid (or) how much do cyber security get paid ?
- Depending on the position, interns may or may not be paid. Unpaid internships are common, particularly when the internship amounts as academic credit toward graduation. For an internship to qualify as unpaid, according to the U.S. Department of Labor, both the manager and intern must agree truthful that the internship will be unpaid. There must also be a clear connection between the intern’s educational program and job responsibilities.
- That said, many employers to pay their interns. Some companies recognize there is value in training someone who could become an employee after they graduate college.
- The majority of Fortune 500 companies pay interns, as do jobs in the private sector. Industries where wishful interns can find paid internships include banking, accounting, advertising, public relations, IT, government and fashion.
- cyber security internship salary – The average salary for paid interns is $14.20 per hour, although the salary can range from $6.15 to $20.05 depending on the industry and geographic location.
Cyber Security Interview Questions and Answers
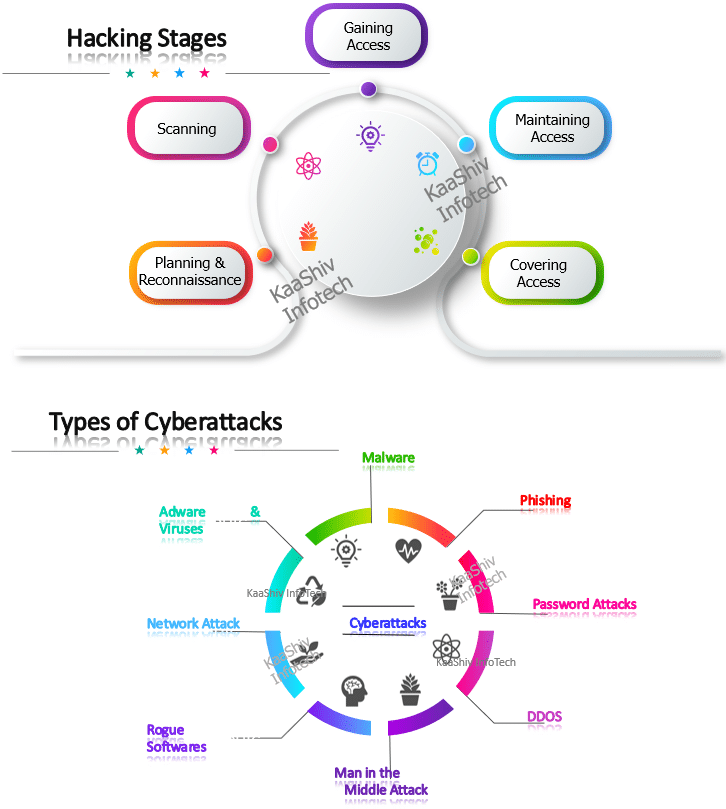
What is cybersecurity ?
- Cybersecurity denotes to the protection of hardware, software, and data from attackers. The main purpose of cyber security is to protect against cyberattacks like accessing, changing, or destroying complex information.
What are the elements of cybersecurity ?
- Information security
- Network security
- Operational security
- Application security
- End-user education
- Business continuity planning
What are the advantages of cyber security ?
- It protects end-users.
- It keeps the business against ransomware, malware, social engineering, and phishing.
- It gives protection for both data as well as networks.
- Cybersecurity stops unauthorized users.
- Increase recovery time after a break.
Define Cryptography
- It is a method used to protect data from third parties called adversaries. Cryptography allows the sender and receiver of a message to read its details.
What is a Firewall ?
- It is a security system designed for the network. A firewall is set on the limits of any system or network which monitors and controls network traffic. Firewalls are used to protect the system or network from viruses, worms, and ,malware. Firewalls also can prevent content filtering and remote access.
Name the different layers of the OSI model.
- Physical Layer
- Data Link Layer
- Network Layer
- Transport Layer
- Session Layer
- Presentation Layer
- Application Layer
What is a VPN ?
- VPN stands for Virtual Private Network. It is a network connection method for making an encrypted and safe connection. This method protects data from intrusion, snooping, restriction.
What is CSRF (Cross Site Request Forgery)? How you can prevent this ?
- CSRF is an attack from a malicious website that will send a request to a web application that a user is previously authenticated against from a different website. To prevent CSRF you can add random challenge token to each request and associate them with user’s session. It makes sure the developer that the request received is from a valid source.
What is ethical hacking ?
- Ethical Hacking is when the individual is allowed to hacks the systems with the authorization to the stock owner to search out of weakness in an exceedingly system and the later fix them.
What are the types of computer based on social engineering attacks ?
Computer based social engineering attacks is,
- Phishing
- Baiting
- Online scams
What is the Network Sniffing ?
- Network Sniffing method is used to monitors data flowing over the computer network links. By allowing you to capture and view the packet to level data on your network, sniffer tool can help you to the find network problems. Sniffers can be used for both stealing data off the network and also for genuine network management.
What are some of the common Cyberattacks ?
- Malware
- Phishing
- Password Attacks
- DDoS
- Man in the Middle
- Drive-By Downloads
- Malvertising
- Rogue Software
What is Phishing ?
- Phishing method includes sending of false emails, chats or website to the copy real system with aim of stealing data from the original website.

